Cybersecurity threats are evolving faster than ever, and small businesses are no longer overlooked. Attackers know that smaller organizations often lack dedicated IT security teams and rely on outdated defenses. For this reason, implementing the right SMB cybersecurity tools has become critical in 2026.
A strong security strategy isn’t just about purchasing software; it’s about choosing tools that address the most common threats efficiently, integrate into your workflow, and reinforce a broader SMB cybersecurity roadmap. With the right tools, small businesses can detect threats, prevent attacks, and protect sensitive data — all without requiring enterprise-level IT teams.
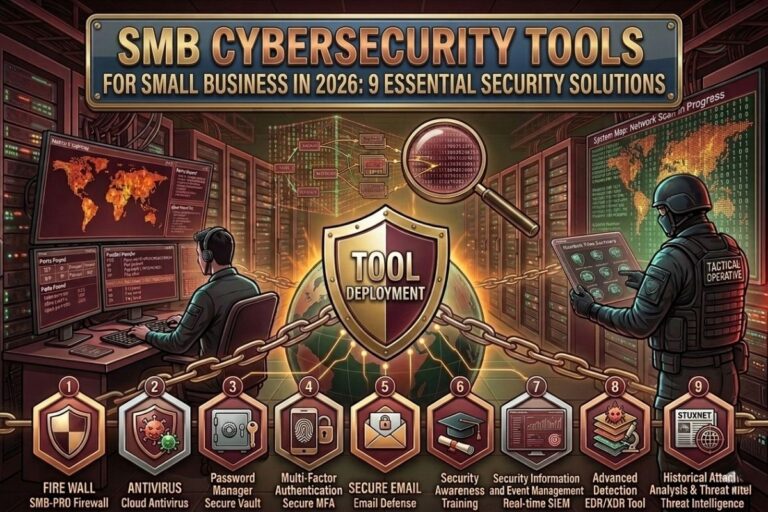
This article explores nine essential SMB cybersecurity tools every small business should deploy in 2026.

1. Endpoint Protection Platforms
Endpoints — including employee laptops, desktops, and mobile devices — are often the first target of attackers. Malware, ransomware, and malicious downloads frequently compromise endpoints, giving attackers a foothold in the network.
Modern endpoint protection platforms go beyond traditional antivirus solutions. They monitor system behavior, detect suspicious activity, and block malicious processes automatically. For small businesses, deploying robust endpoint protection ensures employee devices don’t become gateways for attacks, strengthening the overall SMB cybersecurity tools framework.
2. Firewalls and Network Security
Firewalls remain a fundamental layer of defense. They control network traffic, block unauthorized access attempts, and prevent attackers from reaching sensitive systems.
Next-generation firewalls provide additional capabilities such as intrusion detection, application-level filtering, and real-time monitoring. For small businesses, a properly configured firewall is a simple yet powerful tool that reduces exposure to common attacks. Including firewalls in your SMB cybersecurity tools set ensures your network perimeter is well-defended.
Image Steganography Tool
Hide or extract secret data inside images instantly.
3. Email Security Solutions
Email continues to be one of the most exploited attack vectors. Phishing campaigns, malicious attachments, and impersonation attacks remain highly effective against small businesses.
Email security platforms scan incoming messages to detect malicious content before it reaches employees. Some solutions also block fraudulent senders, warn users about suspicious links, and enforce encryption policies.
Strong email protection is an indispensable part of your SMB cybersecurity tools, significantly lowering the risk of credential theft and malware infections.
4. Multi-Factor Authentication (MFA)
Passwords alone no longer provide adequate protection. Attackers routinely exploit stolen credentials to gain unauthorized access to business systems.
Multi-factor authentication (MFA) adds a secondary verification step, such as a mobile app code, hardware token, or biometric confirmation. Even if a password is compromised, MFA prevents attackers from successfully logging in.
For small businesses, enabling MFA across all critical systems is one of the most effective and low-cost enhancements to any SMB cybersecurity tools strategy.
📌 Recommended Reading
SMB Cybersecurity Policies: 7 Must-Follow Security Rules5. Backup and Disaster Recovery Tools
Ransomware attacks continue to pose major risks, encrypting business-critical data and demanding payment for recovery. Reliable backup and disaster recovery tools are essential SMB cybersecurity tools to mitigate these attacks.
A comprehensive backup strategy includes both local and cloud-based backups. This ensures that data can be restored quickly, minimizing downtime and operational disruption. By integrating backup solutions into your security framework, small businesses can respond effectively to ransomware and other data-loss incidents.
6. Vulnerability Scanners
Software vulnerabilities and misconfigurations are common entry points for attackers. Vulnerability scanners help businesses identify these weaknesses before they can be exploited.
These tools analyze networks, servers, and applications, highlighting outdated software, exposed services, or insecure configurations. Regular scans allow small businesses to address issues proactively, making them a core component of any SMB cybersecurity tools collection.
7. Network Monitoring Platforms
Network monitoring tools provide continuous visibility into system activity. They detect unusual behavior, such as abnormal data transfers or repeated login failures, which could indicate a security incident.
Early detection enables rapid response, preventing minor anomalies from escalating into major breaches. For small businesses, network monitoring is a critical addition to SMB cybersecurity tools, ensuring that suspicious activity is identified before it causes serious damage.
8. Identity and Access Management (IAM)
Managing user permissions is vital for minimizing risk. Identity and access management tools allow businesses to control who can access sensitive systems and data.
IAM systems enforce strong authentication policies, implement least-privilege access, and monitor account activity. By ensuring employees only access what’s necessary for their roles, IAM tools reduce the impact of compromised credentials, making them a central pillar of your SMB cybersecurity tools strategy.
9. Security Awareness Training Platforms
Even the best technology cannot eliminate human error. Security awareness training platforms educate employees about phishing, social engineering, and unsafe practices.
Some platforms simulate phishing attacks to measure employee response, reinforcing awareness over time. By combining these programs with technical solutions, small businesses strengthen one of the most critical defensive layers: informed employees.
External Resources
Small businesses can access authoritative guidance through the Cybersecurity and Infrastructure Security Agency (CISA): https://www.cisa.gov/
The OWASP Top Ten Project provides insight into common vulnerabilities and attack methods: https://owasp.org/
Additional insights and cybersecurity research are available at: https://www.filecorrupter.org/
Conclusion
In 2026, small businesses cannot afford to rely on outdated defenses or guesswork. Selecting the right SMB cybersecurity tools ensures organizations can detect threats, protect sensitive data, and respond effectively to cyber incidents.
Endpoint protection, firewalls, email security, multi-factor authentication, backup systems, vulnerability scanners, network monitoring, identity management, and security awareness platforms form a comprehensive toolkit. When these tools are implemented alongside a structured SMB cybersecurity roadmap, small businesses gain the strategic defenses needed to operate safely in an increasingly hostile digital landscape.
😄 Cyber Joke
Why did the small business invest in cybersecurity tools?
Because fixing hacks later costs more than preventing them now! 😄