Ransomware attacks are no longer rare — they’re a daily threat. Small businesses are often targeted because attackers know defenses are usually weaker than at large enterprises, and the potential payout from a successful attack can be significant.
Implementing SMB ransomware prevention strategies is no longer optional. Without a proactive approach, a single compromised system could lead to encrypted data, business disruption, and costly recovery efforts.
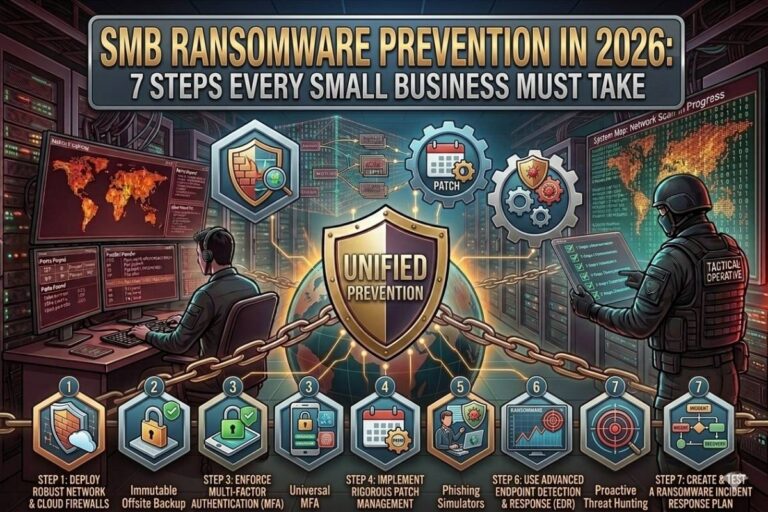
This article outlines seven essential steps for small businesses to prevent ransomware attacks in 2026 and maintain a resilient cybersecurity posture.

Step 1: Conduct a Cyber Risk Assessment
Ransomware prevention starts with understanding the business’s vulnerabilities. An SMB cyber risk assessment identifies critical assets, weak points, and the most likely attack vectors.
By knowing which systems store sensitive data, which are exposed to the internet, and which employees may be most susceptible to phishing attacks, businesses can prioritize controls effectively. Risk assessments are the first step in building any SMB ransomware prevention strategy because prevention starts with awareness.
Step 2: Implement Strong Backup Solutions
Ransomware thrives on disruption. If attackers encrypt business data, the organization can be forced to pay a ransom or risk permanent loss.
Reliable backups are among the most critical SMB ransomware prevention tools. Businesses should implement automated backup systems, including offsite and cloud-based copies, to ensure that essential data can be restored quickly.
Regularly testing backups is also crucial. A backup system that doesn’t work in practice is no better than having no backups at all.
📌 Recommended Reading
SMB Cybersecurity Tools 2026: 9 Essential SolutionsStep 3: Keep Software and Systems Updated
Attackers frequently exploit known vulnerabilities in outdated software to deploy ransomware. Systems, applications, and firmware must be regularly updated with the latest patches.
Including patch management as part of SMB ransomware prevention ensures that attackers cannot leverage known weaknesses. Even a single unpatched system can create an entry point for ransomware.
Automated update solutions can simplify this process, especially for small businesses with limited IT staff.
Step 4: Deploy Endpoint Protection and Detection
Endpoint protection platforms are a cornerstone of modern SMB ransomware prevention. These tools monitor employee devices, detect suspicious activity, and stop malware before it can spread.
Advanced platforms include behavioral analysis to detect ransomware patterns, rather than just relying on signatures. This capability allows small businesses to prevent zero-day ransomware attacks that traditional antivirus solutions might miss.
Step 5: Enforce Email Security and Employee Training
Phishing emails remain one of the primary ransomware delivery methods. Employees often unknowingly click malicious links or download infected attachments.
Effective SMB ransomware prevention combines email security tools with ongoing employee training. Email filters block many malicious messages before they reach employees, while training ensures employees recognize and report suspicious emails promptly.
Simulated phishing exercises can help reinforce awareness and reduce the likelihood of successful attacks.
Image Steganography Tool
Hide or extract secret data inside images instantly.
Step 6: Implement Network Segmentation
Ransomware often spreads laterally once it gains access to a network. Network segmentation limits attackers’ ability to move from system to system.
By isolating critical assets and sensitive data, businesses ensure that even if one system is compromised, ransomware cannot easily infect the entire network. Network segmentation is an essential component of any SMB ransomware prevention strategy in 2026.
Step 7: Develop an Incident Response Plan
Even with all preventive measures in place, it’s possible that ransomware may infiltrate a business. An incident response plan defines how the organization will react to minimize damage.
The plan should include procedures for isolating infected systems, notifying stakeholders, restoring backups, and communicating with external partners. Staff should know their roles and responsibilities in a ransomware incident.
A well-practiced incident response plan ensures that businesses can recover quickly and reduces the impact of an attack on operations.
External Resources
Small businesses can consult authoritative ransomware guidance from the Cybersecurity and Infrastructure Security Agency (CISA): https://www.cisa.gov/
The No More Ransom Project provides free tools and tips to prevent and recover from ransomware attacks: https://www.nomoreransom.org/
Additional insights and SMB security resources are available at: https://www.filecorrupter.org/
Conclusion
Ransomware continues to be a serious threat for small businesses in 2026. Attackers rely on weak defenses, untrained staff, and outdated systems to gain access and cause disruption.
Implementing a proactive SMB ransomware prevention strategy — including risk assessments, backups, system updates, endpoint protection, email security, network segmentation, and an incident response plan — equips small businesses to defend against these threats effectively.
Prevention, preparation, and awareness are the keys. By treating ransomware as a business-critical risk, small businesses can protect operations, data, and reputation from devastating cyber attacks.
😄 Cyber Joke
Why did the ransomware attacker avoid that small business?
Because their backups said, “Nice try!” 😄