There is a fundamental flaw in how most people think about cybersecurity. They assume threats are visible. They assume malicious activity looks suspicious. That assumption is exactly what techniques like steganography are designed to exploit.
Steganography in cybersecurity is not about locking data away. It is about making sure no one realizes the data exists in the first place. Instead of triggering alarms, it blends into normal operations, hiding inside files that are trusted by default.
This is what makes it dangerous. Not complexity. Not sophistication. Silence.
What Steganography Really Means in Cybersecurity
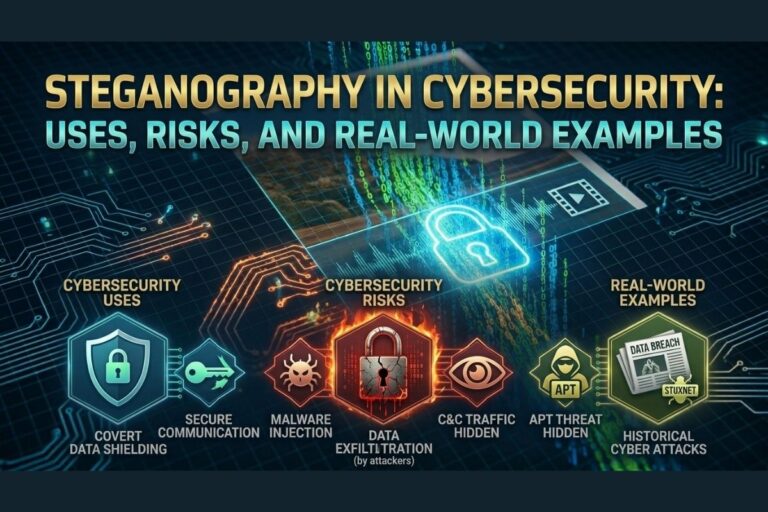
Steganography is the process of embedding hidden information inside a carrier file such as an image, audio clip, or video. In cybersecurity, this technique is used to conceal communication, mask data movement, and bypass detection systems that rely on visible indicators.
Unlike encryption, which signals that protected data is present, steganography removes that signal entirely. A file containing hidden data appears identical to a clean file. It opens normally, functions normally, and raises no immediate suspicion.
That distinction is what allows steganography in cybersecurity to operate in environments where traditional defenses focus on known threats and observable anomalies rather than concealed data structures. Security organizations such as OWASP continue to highlight the importance of understanding unconventional attack vectors that bypass standard detection methods.
📌 Recommended Reading
Types of Steganography: Image, Audio & Video ExplainedLegitimate Uses of Steganography
Steganography is not inherently malicious. In controlled environments, it serves legitimate and valuable purposes.
Organizations use steganography to protect sensitive communications by embedding data within benign files. This approach can reduce the likelihood of interception because the transmission itself does not appear significant.
It is also used for digital watermarking, where identifying information is embedded into media files to verify ownership or authenticity. In this context, steganography provides a layer of integrity rather than concealment for malicious intent.
In research and security testing, steganography is used to simulate advanced attack techniques. This allows defenders to understand how hidden data moves through systems and where detection mechanisms fail.
The technique itself is neutral. The application defines the risk.
How Attackers Use Steganography
The same properties that make steganography useful also make it effective for offensive operations.
Attackers use steganography to embed malicious payloads within image files, allowing those files to pass through filters that would normally block executable content. Once inside a system, the hidden data can be extracted and executed.
Another common use involves command and control communication. Instead of sending instructions directly, attackers hide commands within files hosted on external servers. Compromised systems retrieve these files, decode the hidden instructions, and execute them without triggering obvious network alerts.
Data exfiltration is another critical use case. Sensitive information can be embedded into images or other media files and transmitted out of an organization without detection. Because the files appear legitimate, the transfer often goes unnoticed.
This is where steganography in cybersecurity becomes a serious problem. It allows malicious activity to exist within normal traffic patterns.
Image Steganography Tool
Hide or extract secret data inside images instantly.
Real-World Examples of Steganography in Action
Steganography is not theoretical. It has been observed in multiple real-world scenarios.
Malware campaigns have used image files to conceal malicious code, distributing them through compromised websites and phishing emails. The images appear harmless, but once processed by infected systems, the hidden payload is revealed and executed.
Threat actors have also used steganography to maintain persistence within a network. By storing encoded instructions inside external media files, they can update or modify behavior without deploying new malware, reducing the risk of detection.
In some cases, stolen data has been embedded into image files and uploaded to public platforms. From a monitoring perspective, this looks like normal user activity. In reality, it is a covert data transfer operation.
If you want to understand how these techniques work in practice, you can explore and test them directly using your own platform:
https://www.filecorrupter.org
The Risks and Security Implications
The primary risk of steganography in cybersecurity is that it bypasses assumptions. Most security systems are designed to detect anomalies, not hidden data within legitimate file formats.
Image files, audio files, and video content are generally trusted. They are rarely subjected to deep inspection at the binary level. This creates an opportunity for hidden data to move freely within environments that appear secure on the surface.
Detection requires specialized analysis techniques, including statistical evaluation of file structures and comparison against expected data patterns. These methods are not commonly implemented in standard security tools, which means many organizations remain exposed.
The increasing availability of steganography tools also lowers the barrier to entry. Techniques that once required advanced knowledge are now accessible through simple interfaces, expanding the potential for misuse.
Final Thoughts
Steganography in cybersecurity forces a shift in perspective. It challenges the idea that visibility equals security.
A file does not need to look malicious to be dangerous. It only needs to carry something that was never meant to be seen.
Understanding how steganography works is not about curiosity. It is about awareness. The more you rely on what is visible, the more vulnerable you become to what is hidden.
And in a landscape where attackers prioritize stealth over noise, the most effective threats are the ones that never reveal themselves.
😄 Cyber Joke
Why do hackers love steganography?
Because the best secrets are the ones no one knows exist! 😄