Most people think of steganography as a niche concept—something technical, obscure, and rarely used. That assumption is wrong.
Understanding the types of steganography is critical because the technique is not just about hiding data. It is about hiding intent. Steganography allows information to move through systems without triggering suspicion, which makes it valuable in environments where detection matters more than encryption.
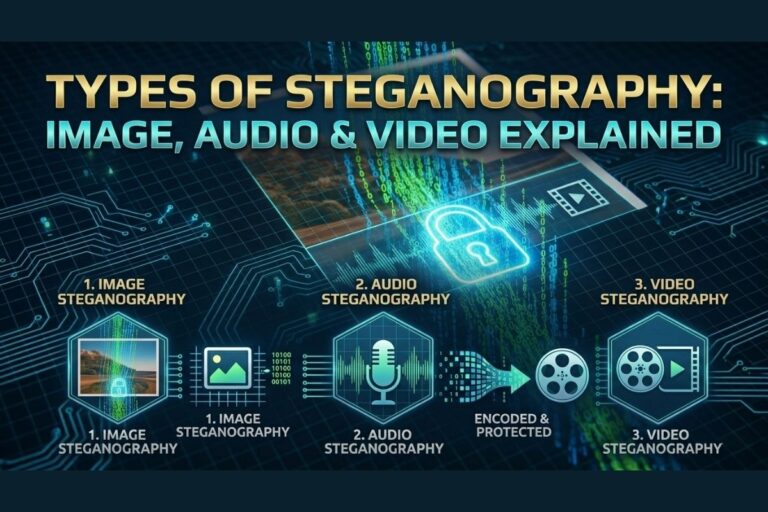
Types of Steganography Explained
Steganography is the process of embedding hidden data inside a carrier file in a way that conceals the existence of that data. Unlike encryption, which protects the content of a message, steganography removes the signal that a message exists at all.
To properly understand the types of steganography, it is necessary to examine how different file formats behave when manipulated. Images, audio files, and video containers all store data differently, which directly affects how hidden information can be embedded and later recovered.
Security organizations such as OWASP emphasize the importance of understanding unconventional attack vectors. Steganography remains one of the most overlooked techniques because the data transfer itself often appears completely normal.
📌 Recommended Reading
What is Image Steganography & How Does It Work?Image Steganography
Image steganography is the most commonly used method among the types of steganography. It works by modifying the binary structure of image files, typically through least significant bit (LSB) manipulation. Because digital images contain thousands or even millions of pixels, they provide a large environment where small modifications can be made without visibly altering the image.
These minor modifications are usually invisible to the human eye. Changing a single bit within a pixel rarely produces a noticeable visual difference, but across thousands of pixels those changes can encode a significant amount of hidden data.
This is why the ability to hide message in image files and later extract hidden image data from image samples has become a practical demonstration of how easily visual media can be manipulated. Among the different types of steganography, image-based approaches remain the most accessible due to their balance of simplicity, storage capacity, and reliability.
If you want to see this technique demonstrated in a controlled environment, you can test it directly here:
https://www.filecorrupter.org
Audio Steganography
Audio steganography represents a more delicate approach compared to other types of steganography. Instead of altering visual data, the technique modifies sound signals in ways that remain difficult for the human ear to detect.
Common approaches involve manipulating frequencies, phase shifts, or echo patterns inside the waveform. Because human hearing is less sensitive to minor changes in certain sound frequencies, these adjustments can conceal hidden data without noticeably affecting audio quality.
Image Steganography Tool
Hide or extract secret data inside images instantly.
However, audio steganography requires precision. Unlike images, audio signals can become distorted if the modifications are too aggressive. This makes the process more technically demanding, but when implemented correctly it can be extremely difficult to detect.
Video Steganography
Video steganography is the most complex implementation among the types of steganography. A video file is essentially a sequence of images combined with synchronized audio. This structure creates multiple opportunities for embedding hidden data across different layers of the file.
Data can be concealed within individual frames, distributed across motion vectors, or hidden within the audio track itself. Because video files are typically large and contain thousands of frames, the potential storage capacity for hidden information increases significantly.
These characteristics make video files an attractive medium for concealment. Among the types of steganography, video-based methods offer the greatest flexibility because hidden data can be dispersed across multiple components of the file.
Key Differences Between the Types
The differences between the types of steganography largely depend on how each medium handles data.
Image files offer simplicity and capacity, making them ideal for demonstrating the basic principles of hidden data embedding. Audio files introduce additional complexity because sound distortion must be avoided. Video files combine multiple layers of information, which expands both the potential storage capacity and the difficulty of detection.
Understanding these distinctions helps security professionals identify how hidden data might be transmitted within seemingly harmless media files.
Final Thoughts
The types of steganography are not defined by the media formats themselves, but by how those formats can be manipulated to conceal information.
Images, audio recordings, and videos are trusted file types that move across networks every second. That trust is exactly what makes them effective carriers for hidden communication.
If you only analyze what appears on the surface, you miss what may be hidden underneath—and in cybersecurity, the threats that matter most are often the ones that never reveal themselves.
😄 Cyber Joke
Why did the hacker use steganography?
Because hiding secrets in plain sight is the best camouflage! 😄