Every year, cyber attacks become more aggressive, more automated, and more profitable for attackers. Small businesses are no longer ignored. In fact, they are often preferred targets because attackers know security controls are usually weaker and response capabilities are limited.
This is why building an SMB cybersecurity roadmap is no longer optional. It is one of the most important strategic decisions a small business can make.
Without a clear security strategy, organizations often rely on scattered tools, inconsistent policies, and reactive responses to threats. That approach leaves gaps that attackers can easily exploit. A well-designed SMB cybersecurity roadmap provides structure. It helps businesses identify risks, prioritize security improvements, and build stronger defenses over time.
If a company wants to operate safely in 2026, it needs a plan. Cybersecurity cannot be random.
What an SMB Cybersecurity Roadmap Actually Is
An SMB cybersecurity roadmap is a structured plan that outlines how a small business will protect its systems, networks, and sensitive data from cyber threats.
Instead of reacting to security problems after they appear, the roadmap creates a strategic path for strengthening security in stages. It defines what assets must be protected, what threats exist, and what defensive controls should be implemented to reduce risk.
Many businesses mistakenly believe cybersecurity is simply about purchasing software. Firewalls, antivirus tools, and monitoring systems are important, but they are only effective when they are deployed as part of a larger strategy. A proper SMB cybersecurity roadmap ensures every security control has a clear purpose and supports the organization’s broader protection goals.
The roadmap becomes the foundation for how the organization approaches cyber defense.
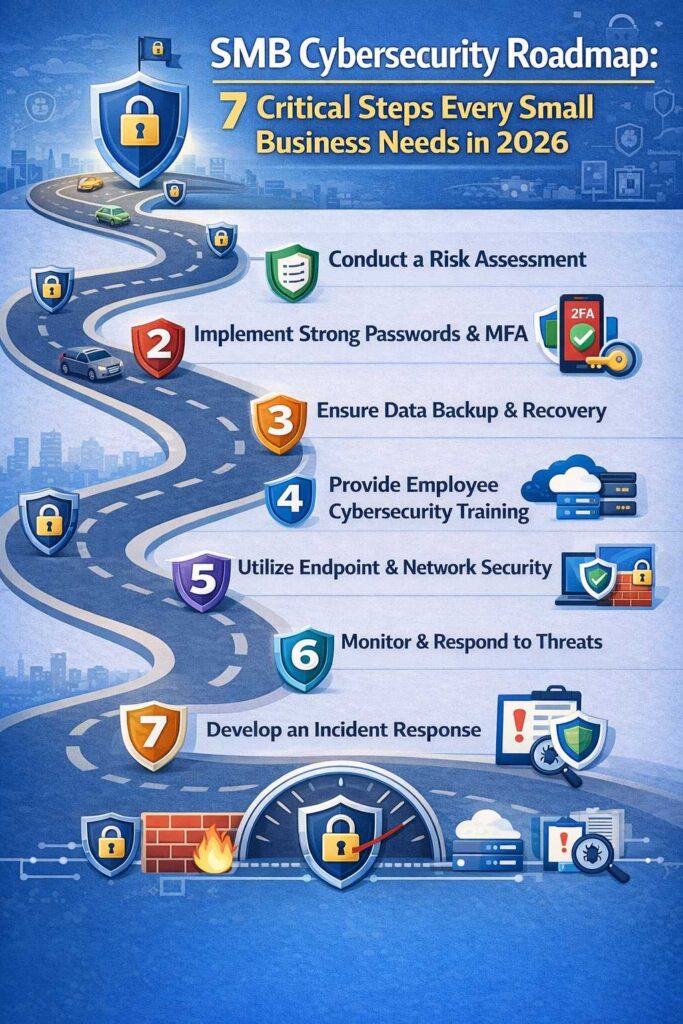
Step 1: Identify Critical Assets for Your SMB Cybersecurity Roadmap
The first step in building an SMB cybersecurity roadmap is identifying the digital assets that keep the business running.
Every organization relies on systems that store or process sensitive information. These systems may include customer databases, payment processing platforms, accounting software, internal communication tools, and cloud applications used for daily operations.
If attackers gain access to these assets, the consequences can be severe. Data theft, financial fraud, operational disruption, and reputational damage are common outcomes.
Businesses should create a complete inventory of their digital infrastructure. This includes servers, employee devices, cloud platforms, and third-party software services. Many security gaps exist simply because organizations lose track of what systems they actually use.
An accurate asset inventory ensures the SMB cybersecurity roadmap focuses on protecting the resources that matter most.
Step 2: Conduct Risk Analysis for Your SMB Cybersecurity Roadmap
After identifying critical assets, the next stage of the SMB cybersecurity roadmap is understanding the risks those assets face.
Cyber threats come from many directions. External attackers constantly scan the internet searching for exposed systems, weak authentication controls, and outdated software. Automated scanning tools can identify vulnerable targets within minutes.
Phishing campaigns remain one of the most common attack methods. Employees receive convincing emails designed to trick them into revealing login credentials or downloading malicious files. Once attackers gain access to an internal account, they often move laterally across the network.
Internal risks must also be considered. Misconfigured cloud storage, weak password policies, and unsecured remote access systems can expose sensitive data even without an external attacker.
A thorough risk analysis allows organizations to prioritize which vulnerabilities must be addressed first within the SMB cybersecurity roadmap.
Step 3: Security Policies That Strengthen Your SMB Cybersecurity Roadmap
Technology alone cannot protect a business. Security policies play a crucial role in any SMB cybersecurity roadmap because they define how employees interact with company systems.
Clear policies reduce risky behavior and create consistent expectations across the organization. For example, password policies should require strong authentication practices and discourage password reuse. Remote access policies should require secure connections and multi-factor authentication.
Employees should also understand how to handle sensitive information, how to recognize suspicious emails, and how to report potential security incidents.
When policies are clearly defined and communicated, employees become an active part of the organization’s security posture rather than an accidental vulnerability.
📌 Recommended Reading
SMB Ransomware Prevention in 2026Step 4: Technology That Supports Your SMB Cybersecurity Roadmap
The next step in the SMB cybersecurity roadmap involves deploying security technologies that protect systems from common attack methods.
Endpoint protection platforms help detect malware, ransomware, and suspicious activity on computers and servers. Network firewalls control traffic entering and leaving the organization’s network, preventing unauthorized access attempts.
Email security tools are particularly important because phishing remains a primary attack vector. Filtering systems help identify malicious attachments and suspicious links before they reach employees.
Backup systems are another critical component of a strong SMB cybersecurity roadmap. If ransomware compromises company data, reliable backups allow the organization to restore operations without paying attackers.
These technical controls create the defensive layers that make successful attacks far more difficult.
Step 5: Employee Training in an SMB Cybersecurity Roadmap
Human error is one of the most common causes of security incidents. Attackers frequently target employees because manipulating people is often easier than breaking through technical defenses.
For this reason, security awareness training is an essential element of any SMB cybersecurity roadmap.
Employees should understand how phishing works, how attackers impersonate trusted contacts, and how malicious websites attempt to steal login credentials. Training should also teach employees how to verify suspicious requests before responding.
When employees learn to recognize these tactics, they become a powerful defensive layer. Instead of unknowingly assisting attackers, they help identify threats early.
Step 6: Monitoring and Detection in an SMB Cybersecurity Roadmap
Cybersecurity is not a one-time project. Threats evolve constantly, and new vulnerabilities are discovered every week. A strong SMB cybersecurity roadmap includes continuous monitoring so suspicious activity can be detected quickly.
Monitoring tools track login activity, network traffic, and unusual system behavior. Security logs record events that allow administrators to investigate potential incidents.
Regular vulnerability scanning is also important. Scanning tools identify outdated software, exposed services, and configuration errors that attackers might exploit.
By maintaining visibility into their systems, businesses can respond to threats before they escalate into major incidents.
Image Steganography Tool
Hide or extract secret data inside images instantly.
Step 7: Incident Response in an SMB Cybersecurity Roadmap
Even the most secure organizations must prepare for the possibility of a cyber incident. This is why every SMB cybersecurity roadmap should include a clear incident response strategy.
An incident response plan defines what actions must be taken when a security event occurs. It identifies who is responsible for responding, how systems should be isolated, and how data recovery will be performed.
Organizations that prepare for incidents respond far more effectively than those that attempt to improvise during an attack. Preparation reduces downtime, limits damage, and helps businesses recover quickly.
Cybersecurity guidance for small businesses can be found through the Cybersecurity and Infrastructure Security Agency (CISA): https://www.cisa.gov/
Another widely used resource for understanding common security vulnerabilities is the OWASP Top Ten Project: https://owasp.org/
You can also explore additional cybersecurity insights at:https://www.filecorrupter.org/
Conclusion
Cybersecurity threats are not slowing down, and small businesses are increasingly targeted by attackers who know security defenses are often limited.
A structured SMB cybersecurity roadmap helps organizations move from reactive security to strategic protection. By identifying critical assets, analyzing cyber risks, establishing security policies, deploying defensive technologies, training employees, monitoring systems, and preparing for incidents, businesses build a resilient security posture.
In 2026, companies that approach cybersecurity with a clear plan will be far better prepared to withstand the threats that continue to evolve across the digital landscape.
😄 Cyber Joke
Why did the small business create a cybersecurity roadmap?
Because getting lost in cyber threats isn’t a good business plan! 😄