Cyber threats rarely start with dramatic movie-style hacking scenes. In reality, most cyber attacks begin quietly with something much simpler: an exposed vulnerability that nobody noticed.
Small businesses are particularly vulnerable because they often assume attackers are focused on large corporations. That assumption creates dangerous blind spots. Attackers routinely scan the internet looking for weak systems, outdated software, or exposed network services that can be exploited within minutes.
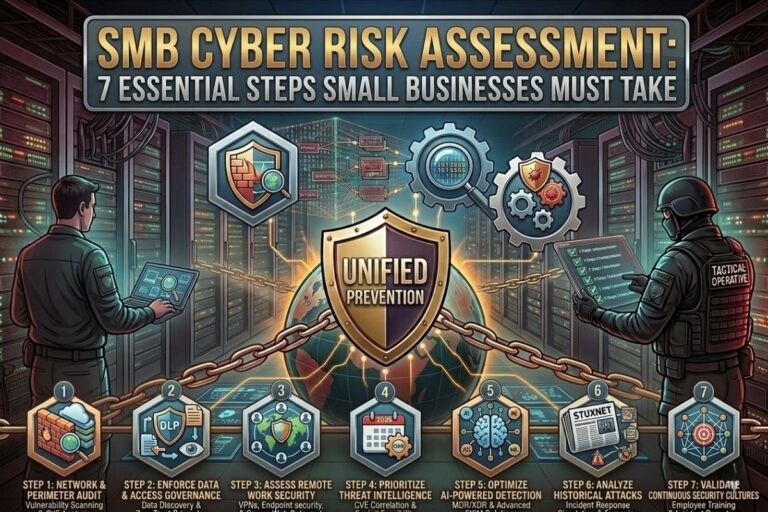
This is why performing a proper SMB cyber risk assessment is one of the most important security practices any organization can implement. Without understanding where the risks are, businesses cannot defend themselves effectively.
A structured SMB cyber risk assessment identifies vulnerabilities, evaluates potential threats, and helps businesses prioritize the security improvements that matter most.
What an SMB Cyber Risk Assessment Actually Does
An SMB cyber risk assessment is a structured process used to identify weaknesses in an organization’s technology environment. Instead of guessing where threats might exist, businesses examine their systems, networks, software, and security practices to determine where attackers might gain access.
The purpose of the assessment is not simply to list problems. The real goal is to understand which risks could cause the greatest damage if exploited. Some vulnerabilities may pose minimal risk, while others could allow attackers to steal customer data, deploy ransomware, or shut down business operations entirely.
A well-executed SMB cyber risk assessment provides clarity. It allows decision makers to focus their cybersecurity investments where they will have the greatest impact.
Step 1: Identify Digital Assets During an SMB Cyber Risk Assessment
The first stage of an SMB cyber risk assessment involves identifying the systems and data that keep the organization running.
Every business relies on critical digital assets. These may include customer databases, financial systems, email platforms, payment processing software, cloud storage environments, and internal collaboration tools.
If attackers compromise these assets, the consequences could include financial losses, operational disruption, and reputational damage.
Businesses should create a detailed inventory of all digital resources used across the organization. This includes employee laptops, servers, cloud platforms, mobile devices, and third-party applications. Many companies underestimate how many systems are actually connected to their networks.
Understanding these assets is the foundation of any effective SMB cyber risk assessment.
Image Steganography Tool
Hide or extract secret data inside images instantly.
Step 2: Identify Threats in an SMB Cyber Risk Assessment
Once critical assets are identified, the next step in the SMB cyber risk assessment process is understanding the threats those assets may face.
Cyber threats come from many sources. External attackers frequently use automated scanning tools to search for exposed systems across the internet. These scans detect open ports, outdated services, and misconfigured servers.
Phishing attacks remain another major threat to small businesses. Employees may receive emails that appear legitimate but contain malicious links designed to steal login credentials.
Insider threats can also create serious security risks. Accidental data exposure, weak passwords, or unsafe file sharing practices can create vulnerabilities without malicious intent.
An effective SMB cyber risk assessment considers both external and internal threat sources.
Step 3: Identify Vulnerabilities in an SMB Cyber Risk Assessment
A vulnerability is any weakness that attackers could exploit to gain access to systems or sensitive data. Identifying these weaknesses is a critical component of an SMB cyber risk assessment.
Common vulnerabilities found in small business environments include outdated software, weak password policies, unpatched operating systems, and unsecured remote access systems.
📌 Recommended Reading
SMB Cybersecurity Roadmap 2026: 7 Critical StepsCloud services are another common source of vulnerabilities. Misconfigured storage buckets or improperly secured access permissions can expose sensitive information to the public internet.
Security scanning tools can help detect these weaknesses automatically, but organizations should also perform manual reviews of critical systems to ensure configurations follow security best practices.
Step 4: Evaluate Risk Levels During an SMB Cyber Risk Assessment
Not all vulnerabilities pose the same level of danger. Some weaknesses may be difficult for attackers to exploit, while others could lead to immediate compromise.
During an SMB cyber risk assessment, each vulnerability should be evaluated based on two factors: the likelihood of exploitation and the potential impact on the organization.
For example, a vulnerability that could expose customer data would typically be considered high risk. A minor software issue affecting a non-critical system might represent a much lower risk.
By ranking vulnerabilities according to their severity, businesses can focus their resources on resolving the most dangerous problems first.
Step 5: Prioritize Security Improvements After an SMB Cyber Risk Assessment
The findings from an SMB cyber risk assessment should lead directly to actionable security improvements.
For many small businesses, this may include implementing stronger authentication controls, updating outdated software, improving network segmentation, or deploying additional monitoring tools.
Security improvements should be prioritized based on the level of risk identified during the assessment. Addressing the most critical vulnerabilities first ensures that the organization reduces its exposure to serious threats as quickly as possible.
This stage often feeds directly into a broader SMB cybersecurity roadmap, which defines how security improvements will be implemented over time.
Step 6: Document Findings From the SMB Cyber Risk Assessment
Documentation is a crucial but often overlooked part of the SMB cyber risk assessment process.
A well-documented assessment provides a clear record of identified vulnerabilities, risk levels, and recommended mitigation strategies. This documentation allows organizations to track progress and demonstrate compliance with security standards if required.
It also helps leadership understand the cybersecurity challenges facing the organization, making it easier to justify security investments and allocate resources effectively.
Without proper documentation, many security improvements lose momentum and important vulnerabilities may remain unresolved.
Step 7: Repeat the SMB Cyber Risk Assessment Regularly
Cybersecurity is never static. New vulnerabilities emerge constantly as software evolves and attackers develop new techniques.
For this reason, an SMB cyber risk assessment should not be performed only once. Organizations should repeat the process regularly to ensure new risks are identified and addressed quickly.
Regular assessments help businesses maintain visibility into their evolving threat landscape and ensure their defenses remain effective over time.
Security is a continuous process, not a one-time project.
External Resources
Small businesses can access cybersecurity guidance from the Cybersecurity and Infrastructure Security Agency (CISA):
Another valuable resource for understanding common security vulnerabilities is the OWASP Top Ten Project: https://owasp.org/
You can also explore additional cybersecurity insights at: https://filecorrupter.org/
Conclusion
Small businesses face an increasingly aggressive cyber threat landscape, and many attacks succeed simply because organizations fail to identify their vulnerabilities before attackers do.
A structured SMB cyber risk assessment helps businesses understand where their weaknesses exist and how those weaknesses could be exploited. By identifying assets, evaluating threats, discovering vulnerabilities, prioritizing improvements, and repeating the process regularly, organizations gain the visibility needed to strengthen their defenses.
Cybersecurity begins with awareness. When businesses take the time to conduct a thorough SMB cyber risk assessment, they take the first major step toward building a stronger and more resilient security posture.
😄 Cyber Joke
Why did the small business finally do a cyber risk assessment?
Because guessing security risks is not a smart investment! 😄