The modern internet is built on millions of servers, devices, and services that communicate through network ports. Every time a system connects to the internet, it exposes certain services that allow data to flow between computers. In many cases, these services are intentionally public. Web servers, email servers, and remote services must communicate openly to function.
The problem begins when systems expose services that were never meant to be public. Misconfigurations, outdated infrastructure, and overlooked network changes can leave systems visible to anyone scanning the internet.
This is where Shodan port scanning becomes important to understand.
Unlike traditional search engines that index websites, Shodan indexes internet-connected devices. It continuously scans IP ranges across the globe, recording the services that respond on open ports. Those responses reveal information about the systems running behind them.
For security professionals, this visibility can help identify exposure before attackers exploit it. For attackers, however, the same information provides a map of potential targets.
Understanding how Shodan port scanning works is essential for anyone responsible for protecting modern infrastructure.
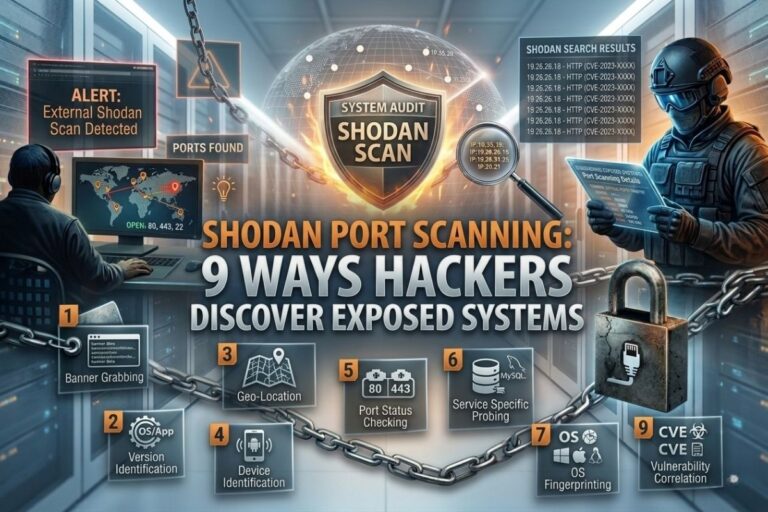
Understanding Shodan Port Scanning
A proper understanding of Shodan port scanning begins with understanding how internet services operate.
Every network service communicates through a numbered port. When a device listens on a port, it waits for incoming connections. If a connection request arrives, the system responds with data describing the service running on that port.
This response is commonly known as a service banner.
Service banners often reveal details about the software running on a device. Information such as the server type, software version, and configuration settings may be included in the response.
Shodan collects these responses by scanning the internet and recording which devices reply on specific ports. The platform stores this data and makes it searchable through its database.
Instead of searching for web pages, users can search for exposed services, server technologies, and connected devices.
This ability to identify systems based on open services is what makes Shodan such a powerful reconnaissance tool.
Why Shodan Port Scanning Matters in Cybersecurity
The visibility created by Shodan port scanning highlights a major reality of cybersecurity: systems connected to the internet are rarely invisible.
Organizations sometimes assume that their internal infrastructure is hidden simply because they have not publicly advertised it. In practice, if a service responds to the internet, it can often be discovered by automated scanning tools.
Shodan simplifies this discovery process by maintaining a continuously updated database of exposed systems.
Security teams can use the platform to search for their own infrastructure and identify services that appear publicly accessible. If unexpected systems appear in the results, administrators can investigate and correct the issue.
Attackers, however, use the same data to locate vulnerable targets.
📌 Recommended Reading
Shodan Tutorial Cybersecurity: 10 Powerful Searches Security Professionals UseBy identifying exposed technologies and outdated software versions, attackers can narrow their focus to systems that may be easier to compromise.
This is why visibility into open ports and internet-facing services is critical for defensive security.
How Hackers Use Shodan Port Scanning
Attackers rarely launch an attack blindly. Instead, they begin by gathering information about potential targets. This phase is known as reconnaissance.
Shodan port scanning dramatically simplifies reconnaissance because the platform has already performed much of the scanning work.
An attacker searching Shodan might look for specific technologies known to contain vulnerabilities. For example, they might search for outdated server software or exposed administrative interfaces.
If those systems appear in the results, the attacker can begin analyzing them further.
Once a potential target is identified, attackers may attempt additional actions such as password attacks, vulnerability exploitation, or deeper network probing.
In many cases, the weakness is not a sophisticated vulnerability but a simple configuration error. Systems left exposed to the internet without proper authentication or security controls are common targets.
Understanding how attackers use reconnaissance tools helps organizations defend against them.
Common Services Discovered Through Shodan Port Scanning
A Shodan port scanning search can reveal a surprising variety of technologies connected to the internet.
Web servers are among the most common discoveries. Because these systems are designed to be publicly accessible, they frequently appear in search results. However, older web server versions sometimes remain online long after security updates are released.
Remote access services are another common exposure. Administrative protocols used for remote system management occasionally appear online without strong authentication controls.
Databases are also frequently discovered. Misconfigured database servers may allow external connections when they were intended to remain internal.
Internet-connected cameras and IoT devices appear in large numbers as well. Many of these devices operate with default credentials or outdated firmware that has not been updated by users.
Network infrastructure occasionally appears in results as well. Routers, firewalls, and management interfaces sometimes expose configuration portals that administrators assumed were private.
Each of these exposures can provide attackers with information about the technology running inside an organization.
The Security Risks of Exposed Ports
The information revealed through Shodan port scanning often leads to one important conclusion: open services increase attack surface.
Every exposed port represents a potential interaction point between a system and the outside world. If that service contains vulnerabilities or weak authentication controls, attackers may attempt to exploit it.
Even when a vulnerability does not exist, attackers may attempt brute-force authentication attempts or social engineering campaigns targeting administrators responsible for the system.
Outdated services present an even greater risk. Software that has not been updated may contain publicly known vulnerabilities that attackers can exploit using automated tools.
In many cases, the exposure itself becomes the primary weakness.
Organizations frequently discover services that were accidentally exposed during infrastructure changes, testing environments, or cloud deployments. These forgotten systems often remain online for long periods without monitoring or security updates.
Reducing these exposures significantly improves an organization’s defensive posture.
Using Shodan Port Scanning Defensively
Although Shodan port scanning is often associated with offensive security research, it can be extremely valuable for defensive teams as well.
Security professionals can perform searches to determine what systems associated with their organization appear publicly accessible. If unexpected assets appear, administrators can investigate the cause.
This process helps identify misconfigurations, forgotten servers, or cloud resources that were unintentionally exposed.
Shodan can also assist with vulnerability management. When a vulnerability is discovered in a widely used technology, security teams can search Shodan to determine whether systems using that technology appear in their environment.
By combining external visibility with internal monitoring, organizations gain a more accurate understanding of their attack surface.
This proactive approach helps reduce the likelihood that attackers will discover vulnerable systems first.
External Cybersecurity Resources
Security professionals interested in learning more about Shodan can explore the official platform:
Guidance on protecting internet-connected infrastructure can also be found through the Cybersecurity and Infrastructure Security Agency (CISA):
These resources provide valuable information about identifying and securing exposed services.
Conclusion
Understanding Shodan port scanning provides insight into how internet-connected systems become visible to both defenders and attackers.
By continuously scanning global networks and indexing service responses, Shodan reveals the technologies that power the modern internet. While this visibility can be used for reconnaissance, it also provides organizations with an opportunity to discover their own exposures.
Systems connected to the internet inevitably leave digital fingerprints. The key to strong cybersecurity is recognizing those fingerprints and ensuring they do not reveal unnecessary information about the infrastructure behind them.
When organizations monitor exposed services, update outdated systems, and limit unnecessary network access, the data revealed through scanning tools becomes far less useful to attackers.
In that sense, understanding Shodan is not simply about reconnaissance. It is about learning how the internet sees your infrastructure—and ensuring that what it sees does not become a security risk.
😄 Cyber Joke
Why did the hacker love port scanning?
Because it’s like ringing every doorbell until someone forgets to lock the door! 😄